Hosting your own website looks simple for those of us who have some technical skills. And it is. You could be up and running in an hour or so, hosting your own website on a computer in your office or at home, using the existing internet and computer.
It’s true, the basics are simple. You set up a web server, a database server, configure access to the computer in the router, point the DNS to your public IP and your website is online.
But like with all good things, most of the work is in the details.
I will try to compile a list of things that a web hosting provider thinks about (or should think about):
- Loading Speed: Google research shows that half of the visitors of the typical website drop off while they’re waiting for the website to load. Speed is a combination of how the website’s built, server hardware, server resources (such as processor power, memory etc.), software configuration, domestic/international bandwidth, server location, use of CDN etc. The choice of your web host and the plan you have with them affect many of these factors and thus the loading speed and your website’s revenue.
- Backup and restore options: Computers and harddisks crash, so what about those orders that came in today, are they gone too? Was the backup on the same server? Or were they stored off site? What about the backup from last month?
- Internet Connection: Regular internet providers (cable/dsl) to your home or office can typically download well, but have limitations. Especially with uploads. Your website gets uploaded to visitors, and that bandwidth is shared amongst all visitors, so a typical internet provider doesn’t provide enough bandwidth for your visitors. It’s also not reliable and when it’s down, your website and business is down too.
- Software updates: The minimum to keep your website somewhat secure is keeping the server software up to date. Testing if the updates work well are required too.
- Software configuration: The default settings of server software leaves a lot of holes for hackers to break in, also the default settings do not provide you with the best performance. Expert knowledge/experience is required to make changes to the configuration to make sure it works well for the specific hosting solution that is required.
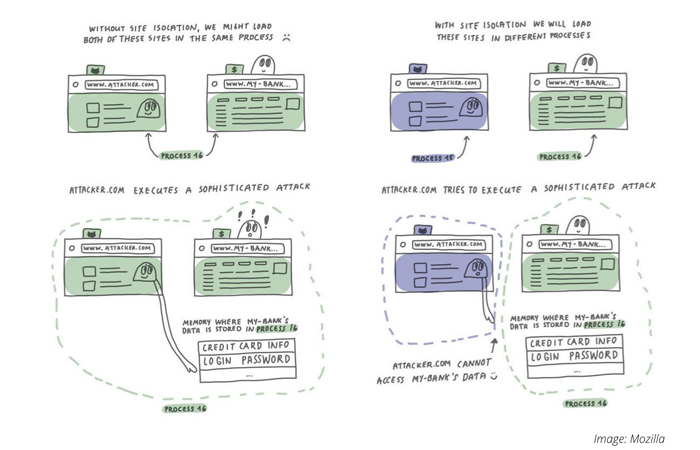
- Firewall/Malware/Anti-virus Scanning: An ever increasing number of automated programs (bots) is trying to find holes in the websites themselves. When they succeed, the customer’s website is used to send spam, show embarrasing advertisements etc. Scanning websites and preventing access means website owners can be protected or at least alerted to fix the issues before their Google ranking is affected and negatively affects the business revenue.
- Support: Having deep knowledge and experience about hosting is something that accrues within a good web host over the years. Having access to that experience via email or over the phone is priceless.
When you host not from your home or office, but from a cloud provider such as Amazon AWS or Microsoft Azure, you at least have item #3 covered, the internet connection. All the other items still rely on your own technical skills to set up, develop and keep up to date.
When you should host your own website (or application):
- If your business is your website: for example if you’re eBay or Facebook (and this is not about the size of the business, but the core of the product) and web hosting is at the core of your product. The flexibility of in-house hosting gives you a competitive edge.
- When you have all of the above in house: an experience web hosting team, the software solutions and adding this complexity to your business is worth it.
- When you don’t care [about any of the above]. That’s fine. Just please keep things up to date so you don’t help spammers.
If you have feedback to add to the list please let us know.
If you need quality hosting in Bangkok, please fill out the form below so we can see how we can best work together.